Cryptocurrencies, with their decentralized nature and promise of privacy, have witnessed rapid expansion over the years. However, as the ecosystem has grown, so have the tools and services that aim to enhance the privacy and anonymity of crypto transactions. One such service that has garnered attention is the cryptocurrency mixer, also known as a tumbler.
What is a Cryptocurrency Mixer?
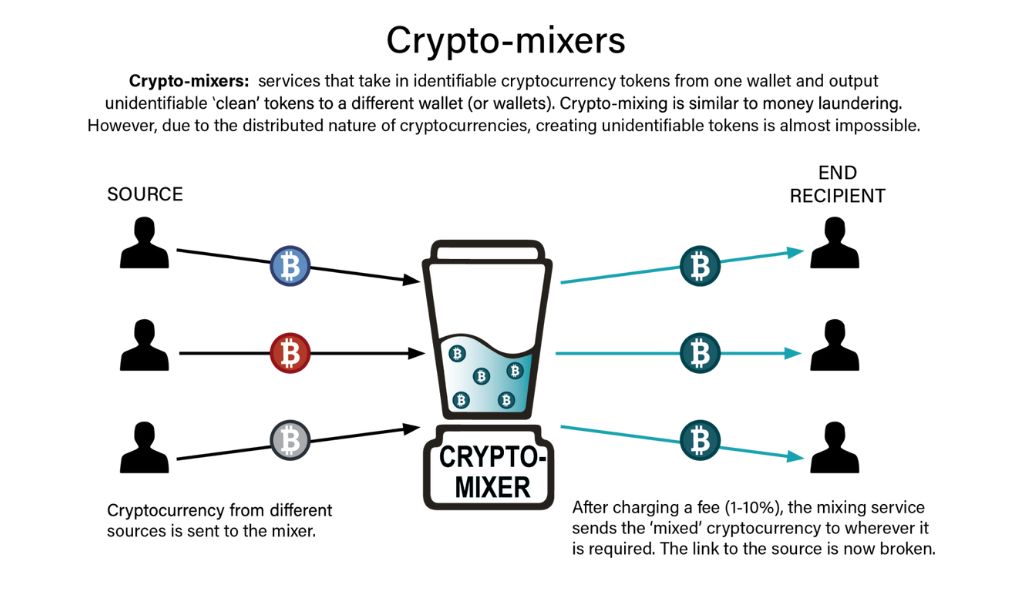
A cryptocurrency mixer, or tumbler, is a service that mixes potentially identifiable cryptocurrency funds with a vast pool of other funds. The primary objective is to enhance the privacy of transactions by making the origins of a particular transaction harder to trace. This is achieved by breaking the direct link between the sender and receiver addresses, making the transaction trail convoluted.
Why Use a Mixer?
Many individuals and entities use crypto mixers to maintain the privacy of their cryptocurrency transactions. These services do not typically require Know Your Customer (KYC) checks, making them attractive for those who prioritize anonymity. However, this very feature also makes them susceptible to misuse, such as for money laundering or concealing illicit earnings.
Types of Cryptocurrency Mixers
There are primarily two types of mixers:
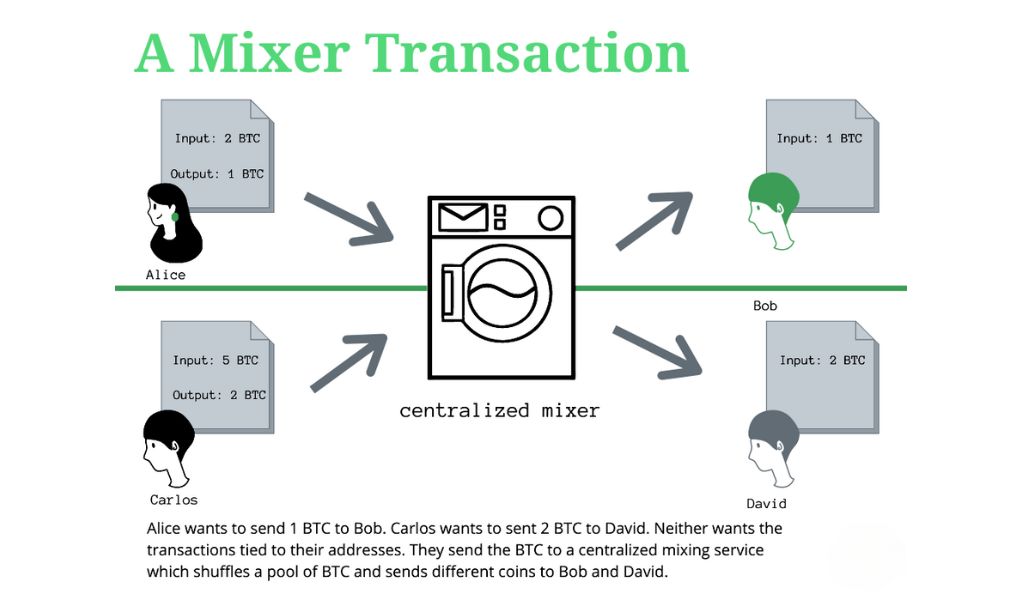
- Centralized Mixers: These are companies that receive Bitcoin (or other cryptocurrencies) and send back a different set of coins for a fee. They offer a straightforward solution for those looking to tumble their coins.
- Decentralized Mixers: These mixers use protocols like CoinJoin to obfuscate transactions. They allow a group of users to pool a certain amount of cryptocurrency and then redistribute it in a manner that conceals the original sources.
- Obfuscation-based Mixers: Also known as decoy-based mixers, they employ techniques to hide a user’s transaction graph. However, with enough resources, it’s possible to reconstruct the transaction graph.
- Zero-knowledge-based Mixers: These rely on advanced cryptographic techniques, like zero-knowledge proofs, to completely erase the transaction graph. Their main limitation is the extensive cryptography involved, which can impact scalability.
Comparison Table: Centralized vs. Decentralized Mixers
| Feature | Centralized Mixers | Decentralized Mixers |
|---|---|---|
| Control | Held by a company | Distributed among users |
| Anonymity Level | Moderate | High |
| Fee Structure | Fixed or percentage-based | Often lower than centralized |
| Trust Level | Requires trust in the company | Trustless, relies on protocol |
How Do Cryptocurrency Mixers Work?
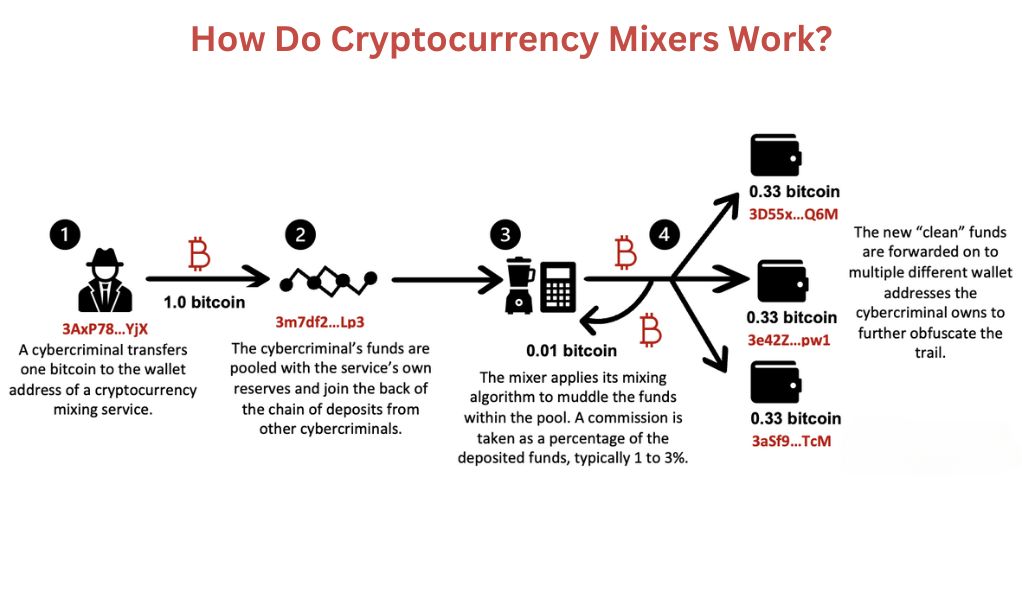
The fundamental concept behind crypto mixers is to route a transaction’s digital signatures through a mechanism that obscures them. In essence, mixers take a user’s cryptocurrency, mix it with a large pool of other cryptocurrencies, and then return smaller units of the crypto to an address specified by the user. The mixing service typically charges a fee, usually between 1-3% of the mixed amount.
Legality of Using Mixers
The legality of using cryptocurrency mixers varies by jurisdiction. In some regions, using mixers to hide transaction trails is considered illegal, especially if the intent is to facilitate illicit activities. In the U.S., for instance, Bitcoin mixers are classified as money transmitters by the Financial Crimes Enforcement Network (FinCEN) and are required to register and obtain necessary licenses.
Can Mixers be Traced?
While mixers are designed to obfuscate transaction trails, it’s not entirely impossible to trace transactions that have been mixed. Advanced tools and techniques can analyze public blockchain data and potentially link transactions to specific individuals or entities. However, the complexity introduced by mixers makes this task challenging.
The Allure of Anonymity in Cryptocurrencies
The rise of cryptocurrencies has brought with it a renewed interest in the concept of anonymity in financial transactions. While traditional banking systems have always been underpinned by the identity of their users, cryptocurrencies introduced a paradigm shift with their decentralized nature and emphasis on privacy. Let’s delve deep into the allure of anonymity in the world of cryptocurrencies.
The Foundations of Cryptocurrency Anonymity
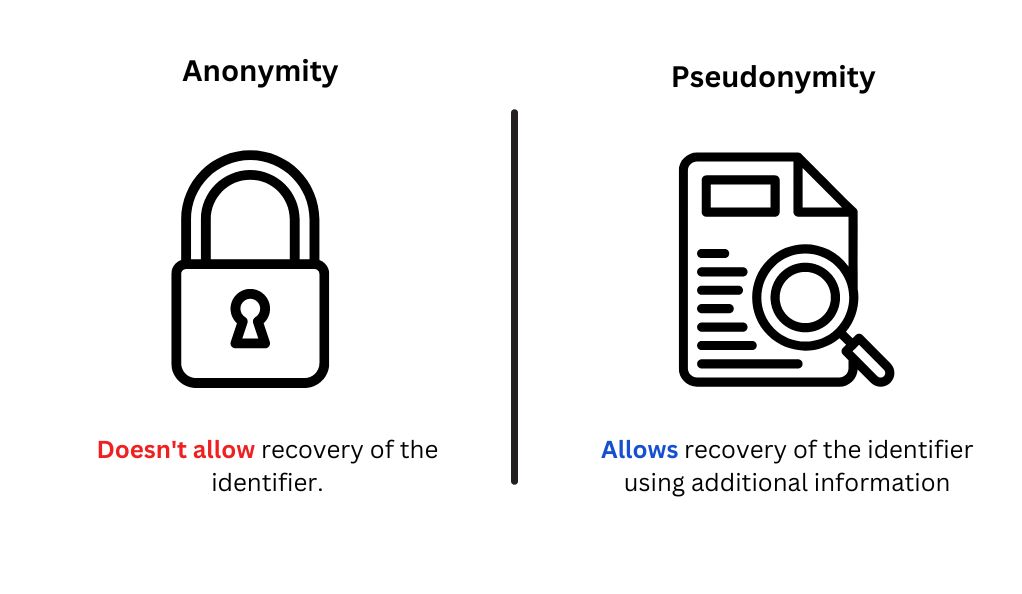
Cryptocurrencies, by design, offer a degree of privacy not seen in traditional financial systems. Each user in the cryptocurrency network is identified not by their personal details but by a pseudonym in the form of a wallet address. This address, while recorded on the blockchain for every transaction, does not directly reveal the identity of the user behind it.
Why Anonymity Matters
The allure of anonymity in cryptocurrencies stems from several factors:
- Privacy Concerns: In an age where data breaches are common, many users are wary of sharing their financial details online. Cryptocurrencies offer a way to transact without revealing personal information.
- Freedom from Censorship: Anonymity ensures that users can make transactions without fear of censorship or sanctions, especially in regions with restrictive financial regulations.
- Protection from Financial Surveillance: With increasing surveillance in banking systems, cryptocurrencies offer a refuge for those who prefer their financial activities to remain private.
The Double-Edged Sword of Anonymity
While anonymity offers many benefits, it also has its downsides:
- Illicit Activities: The privacy offered by cryptocurrencies has made them a preferred mode of transaction for illegal activities, from money laundering to purchasing contraband on the dark web.
- Regulatory Concerns: Governments and regulatory bodies worldwide are concerned about the potential misuse of cryptocurrencies for illicit finance. This has led to calls for stricter regulations and the introduction of Know Your Customer (KYC) checks in crypto exchanges.
Anonymity vs. Pseudonymity
It’s crucial to differentiate between true anonymity and pseudonymity. While all cryptocurrency transactions are recorded on a decentralized ledger (the blockchain), they are linked to wallet addresses and not directly to individual identities. However, with advanced tools and techniques, it’s possible to link wallet addresses to individuals, making the system pseudonymous rather than truly anonymous.
The Future of Anonymity in Cryptocurrencies
The debate around anonymity in cryptocurrencies is ongoing. As regulatory bodies push for more transparency, there’s a parallel development of privacy coins and technologies that offer enhanced anonymity features. The balance between regulatory compliance and user privacy will shape the future of anonymity in the crypto world.
Mechanisms of Mixing Services
Cryptocurrency mixing services have emerged as a pivotal tool for enhancing the privacy of transactions within the blockchain ecosystem. These services aim to obfuscate the transaction trail, making it challenging to trace the origins and destinations of funds. Let’s delve into the mechanisms that underpin these services.
What is a Mixing Service?
A mixing service, often referred to as a tumbler, is designed to enhance the anonymity of cryptocurrency transactions. It achieves this by blending potentially identifiable cryptocurrency funds with a vast pool of other funds, thereby complicating the transaction trail.
The Core Mechanisms of Mixing Services
Based on research and observations, there are primarily two mechanisms employed by mixing services:
- Swapping: This involves the exchange of one set of coins for another. The user sends their coins to the mixing service, which then sends back a different set of coins, effectively breaking the direct link between the input and output addresses.
- Obfuscating: This mechanism is more intricate. It involves blending multiple transactions in such a way that the origins and destinations of funds become intertwined and challenging to decipher.
Transaction-Based Analysis of Mixing Mechanisms
By analyzing transactions on the blockchain, it’s possible to discern the mechanisms employed by various mixing services. For instance, a series of transactions that involve multiple input and output addresses, with varying amounts, might indicate the use of the obfuscating mechanism.
Identifying Mixing Transactions
While mixing services aim to enhance anonymity, certain patterns can be used to identify mixed transactions. For instance, the obfuscating mechanism often involves a series of transactions with multiple inputs and outputs, making them stand out from regular, straightforward transactions. Advanced analytical tools can identify over 92% of such mixing transactions.
Profit Models of Mixing Services
Mixing services typically charge a fee for their services. This fee can be a fixed amount or a percentage of the mixed amount. By analyzing the transaction fees and volumes, it’s possible to estimate the profit margins of popular mixing platforms.
Ethical and Legal Implications
While mixing services offer enhanced privacy, they have also been associated with illicit activities, such as money laundering. This has led to debates around their legality and ethical implications. Some jurisdictions have even classified mixing services as money transmitters, requiring them to adhere to specific regulations.
The Dark Side of Mixing Services
Cryptocurrency mixing services, while designed to enhance the privacy and anonymity of transactions, have also been associated with a range of illicit activities. The decentralized and pseudonymous nature of cryptocurrencies, combined with the obfuscation techniques of mixers, has created a fertile ground for bad actors to exploit. Let’s explore the darker aspects of these services.
The Appeal of Mixing Services
Mixing services, or tumblers, are designed to break the direct link between the sender and receiver addresses in a cryptocurrency transaction. By blending potentially identifiable cryptocurrency funds with a vast pool of other funds, they complicate the transaction trail, making it challenging to trace the origins and destinations of funds.
Illicit Activities and Cryptocurrency
Cryptocurrencies, due to their unregulated nature and high level of anonymity, have become notorious for being preferred by criminals and terrorists for payment and trade. The ability to bypass regulatory limits and avoid detection by authorities has made cryptocurrencies a valuable tool for illicit activities.
The Role of Mixers in Facilitating Crime
Mixers play a significant role in aiding and abetting criminal activities. Some of the crimes associated with cryptocurrency and mixing services include:
- Financing Terrorism: Terrorist organizations have been known to use cryptocurrencies to fund their operations, taking advantage of the anonymity provided by mixers.
- Dark Web Transactions: The dark web, a part of the internet not indexed by search engines, hosts marketplaces where illegal goods and services are traded. Cryptocurrencies, often mixed to hide the transaction trail, are the primary mode of payment.
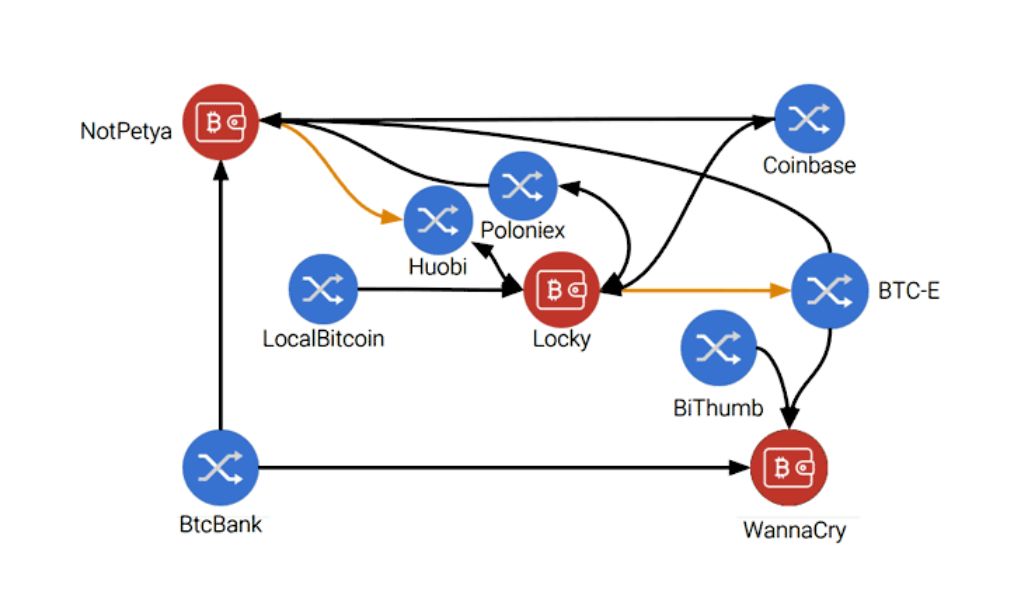
- Ransomware: Cybercriminals who deploy ransomware often demand payments in cryptocurrencies. Once received, these funds are typically mixed to obscure their origin.
- Money Laundering: Criminals use mixers to launder money, making it difficult for authorities to trace the source of illicit funds.
Regulatory Challenges
The rise of illicit activities associated with cryptocurrencies and mixers has caught the attention of regulators worldwide. Many countries are now implementing stricter regulations to curb the misuse of cryptocurrencies. For instance, some jurisdictions classify mixing services as money transmitters, requiring them to adhere to specific regulations.
The Future of Mixing Services
As regulatory bodies push for more transparency in the crypto world, the future of mixing services hangs in the balance. While they offer increased anonymity, the potential for misuse has cast a shadow over their operations. It remains to be seen how the tug-of-war between privacy advocates and regulators will shape the future of these services.
Analyzing Mixing Transactions
Mixing transactions, often referred to as “coin mixers” or “tumblers,” are services that aim to improve the privacy and anonymity of cryptocurrency transactions. They work by pooling together multiple transactions and redistributing them in such a way that it becomes challenging to trace the origin of any specific transaction. This article delves deep into the subject of analyzing mixing transactions, providing a step-by-step guide and highlighting the significance, challenges, and methods used in the process.
Why Analyze Mixing Transactions?
- Forensic Analysis: Law enforcement agencies and investigators might need to trace illicit funds or uncover the activities of malicious actors.
- Regulatory Compliance: Financial institutions may need to ensure that they are not inadvertently facilitating money laundering or other illegal activities.
- Research Purposes: Academics and researchers might analyze mixing transactions to understand the evolving landscape of cryptocurrency privacy techniques.
Challenges in Analyzing Mixing Transactions
- Complexity: Mixers often use sophisticated algorithms to shuffle transactions, making analysis difficult.
- Volume: The sheer number of transactions can be overwhelming, especially when multiple mixers are used in tandem.
- Decoy Transactions: Mixers might add fake transactions to further confuse analysts.
Methods for Analyzing Mixing Transactions
Heuristic Analysis: This involves identifying patterns in transactions. For instance, if multiple inputs of similar amounts are combined into a single transaction, it might indicate a mixing service.
Cluster Analysis: Grouping together addresses that appear to be controlled by the same entity. This can help in identifying the endpoints of a mixing service.
Temporal Analysis: Examining the timing of transactions can sometimes reveal patterns, especially if a mixer consistently outputs transactions at specific intervals.
Comparison of Different Analysis Techniques
| Technique | Advantages | Disadvantages |
|---|---|---|
| Heuristic Analysis | Simple; Can quickly identify patterns | Might produce false positives |
| Cluster Analysis | Effective for large-scale investigations | Requires significant computational power |
| Temporal Analysis | Can reveal time-based patterns | Limited effectiveness on its own |
The Profit Model of Mixing Services
Cryptocurrency mixing services, often referred to as “coin mixers” or “tumblers,” have emerged as a solution for users seeking enhanced privacy in their transactions. By pooling together multiple transactions and redistributing them, these services obfuscate the trail of individual coins, making it challenging to trace their origin. But like any other service, mixers need to be profitable to sustain their operations. This article delves into the profit models adopted by mixing services, shedding light on how they generate revenue while offering privacy-centric services.
Fee Structures in Mixing Services
The primary revenue stream for most mixing services is the fees they charge users. These fees can be structured in various ways:
- Fixed Fee: A set amount charged per transaction, irrespective of the transaction size.
- Percentage-Based Fee: A fee calculated as a percentage of the transaction amount. This is the most common model, with fees typically ranging from 1% to 3%.
- Tiered Fee Structure: Different fee rates applied based on the transaction amount or frequency of use.
Additional Revenue Streams
Apart from transaction fees, some mixers explore other avenues for revenue:
- Affiliate Programs: Mixers might offer referral bonuses to users who bring in new customers.
- Premium Services: Offering faster transaction speeds, enhanced security, or other advanced features for an additional fee.
- Advertisements: Some mixing platforms might host ads, especially if they offer free or low-cost mixing services.
Comparison of Profit Models Among Popular Mixers
| Mixer | Fee Structure | Additional Revenue Streams |
|---|---|---|
| Mixer A | 2% of transaction amount | Affiliate program |
| Mixer B | Fixed fee of 0.001 BTC | Premium services |
| Mixer C | Tiered (1% for <1 BTC, 1.5% for >1 BTC) | Advertisements |
Ethical Considerations and Controversies
The profit model of mixing services is not without its controversies:
Legality: In some jurisdictions, operating or using a mixing service is considered illegal due to concerns about money laundering or other illicit activities.
Trustworthiness: There have been instances where mixing services have run off with users’ funds, leading to concerns about their reliability.
Transparency: Some argue that mixers should be more transparent about their fee structures and operations to gain user trust.
Future of Mixing Services: Challenges and Opportunities
Cryptocurrency mixing services, commonly known as “coin mixers” or “tumblers,” have emerged as a pivotal tool for users seeking enhanced privacy in their transactions. By blending multiple transactions and redistributing them, these services aim to obscure the trail of individual coins, making it difficult to trace their origin. However, as the cryptocurrency landscape evolves, these services face both challenges and opportunities that will shape their future. This article delves into the prospective trajectory of mixing services, highlighting the potential hurdles and the avenues for growth.
The Current Landscape of Mixing Services
Mixing services have grown in popularity as a response to the transparent nature of blockchain transactions. While cryptocurrencies offer a degree of privacy, the public ledger ensures that every transaction can potentially be traced back to its origin. Mixers break this link, offering enhanced anonymity.
Regulatory Challenges
- Illicit Activities: Concerns over money laundering, terrorist financing, and other illegal activities have put mixers under the scanner. Some governments view them as tools that facilitate illicit transactions.
- Global Regulatory Disparity: While some countries have embraced cryptocurrencies, others have imposed strict regulations or outright bans, affecting the operation of mixing services.
- Know Your Customer (KYC) and Anti-Money Laundering (AML): Regulatory pressures may force mixers to implement KYC and AML procedures, potentially compromising user privacy.
Technological Advancements and Opportunities
- Improved Algorithms: As blockchain analysis tools become more sophisticated, mixers will need to adopt advanced algorithms to ensure user privacy.
- Integration with Decentralized Finance (DeFi): The booming DeFi sector offers opportunities for mixers to integrate their services, providing users with both financial tools and privacy.
Environmental Concerns
The energy consumption associated with some cryptocurrencies, particularly Bitcoin, has raised environmental concerns. While mixers themselves may not be energy-intensive, their association with high-energy-consuming cryptocurrencies could pose challenges.
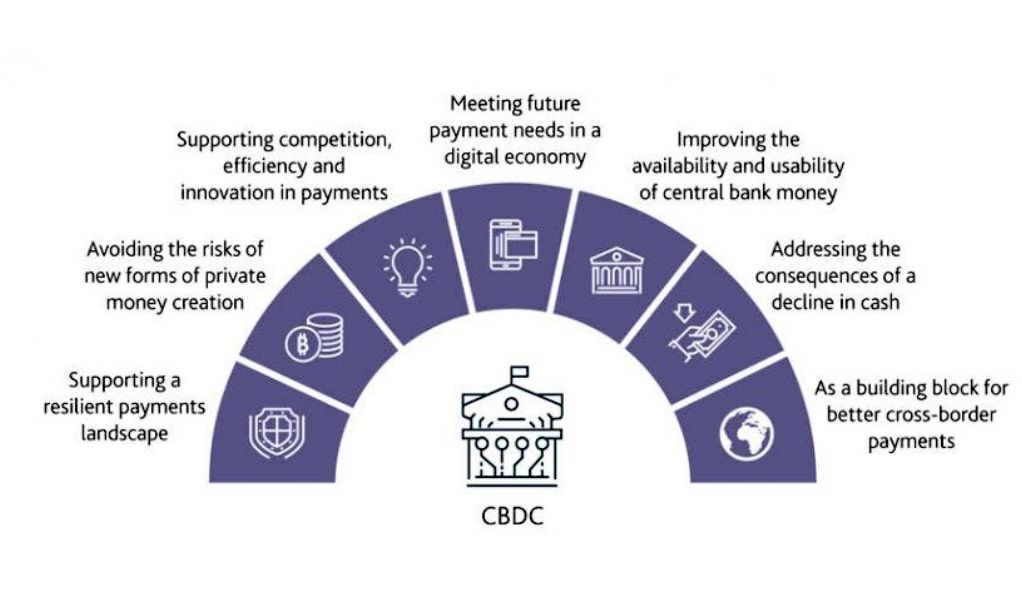
The Rise of Central Bank Digital Currencies (CBDCs)
Many central banks are exploring the idea of launching their own digital currencies. CBDCs could offer the speed and benefits of cryptocurrencies without the associated risks. If CBDCs gain widespread adoption, they could pose a challenge to traditional cryptocurrencies and, by extension, to mixing services. However, if CBDC transactions lack privacy features, there might still be a demand for mixing services.
Case Study: Tracing Stolen Bitcoins
The decentralized nature of cryptocurrencies, combined with the promise of pseudonymity, has made them a prime target for cybercriminals. Bitcoin, being the most popular cryptocurrency, has often been at the center of high-profile thefts. This case study delves into the process of tracing stolen Bitcoins, highlighting the challenges and tools involved in tracking illicit cryptocurrency transactions.
The Initial Response
Upon discovering the breach, the exchange:
- Suspended Transactions: To prevent further unauthorized transfers, the exchange temporarily halted all withdrawals and deposits.
- Notified Authorities: Local law enforcement and cybersecurity agencies were informed of the breach.
- Public Announcement: The exchange informed its users of the breach, assuring them that measures were being taken to trace the stolen funds and enhance security.
Tracing the Stolen Bitcoins
Blockchain Analysis: Every Bitcoin transaction is recorded on a public ledger called the blockchain. Using blockchain analysis tools, investigators were able to trace the movement of the stolen Bitcoins from the exchange’s wallet to multiple other addresses.
Taint Analysis: This method involves tracking the “tainted” coins as they move through the blockchain, allowing investigators to identify wallets associated with the stolen funds.
Heuristic Analysis: By studying patterns and clustering similar transactions, investigators can identify potential wallets owned by the same entity or individual.
Challenges in Tracing
- Coin Mixers: The attackers used coin mixing services to obfuscate the trail of the stolen Bitcoins. Mixers pool together multiple transactions, making it challenging to trace individual coins.
- Cross-Cryptocurrency Trades: Some of the stolen Bitcoins were traded for other cryptocurrencies, adding another layer of complexity to the tracing process.
- Jurisdictional Issues: Cryptocurrencies operate globally, and the stolen funds could be transferred across borders, complicating legal efforts to recover them.
Legal and Regulatory Implications
Legal Action: The exchange pursued legal action against the identified attackers, leading to the arrest and prosecution of two individuals.
Regulatory Response: The theft prompted regulatory authorities to tighten security requirements for cryptocurrency exchanges, emphasizing the need for regular security audits and enhanced user protection measures.
User Reimbursement: The exchange committed to reimbursing affected users, using a combination of its own funds and insurance coverage.
Conclusion
In the ever-evolving digital landscape, the delicate equilibrium between privacy and security remains a paramount concern. On one hand, the demand for privacy underscores the fundamental human right to personal autonomy and freedom from unwarranted surveillance. Conversely, the imperative for security necessitates certain oversight measures to thwart malicious activities and protect societal interests. Striking the right balance is challenging, as excessive privacy can shield malevolent actors, while heightened security can infringe upon individual liberties. As technology advances, the quest continues to harmonize these seemingly opposing forces, ensuring a future where both privacy and security coexist in harmony.
At bitvestment.software, our commitment is to deliver unbiased and reliable information on subjects like cryptocurrency, finance, trading, and stocks. It's crucial to understand that we are not equipped to offer financial advice, and we actively encourage users to conduct their own comprehensive research.
Read More